Anomaly Detection Without a Data Team: How to Spot What Your Dashboards Miss
Last updated: April 2026
Your dashboard says revenue is up 8 percent this quarter. That sounds like good news, and nobody questions it. But buried in the data is a pattern the dashboard doesn’t show: a single enterprise customer placed an unusually large order in March that accounts for almost all of the growth, while your core customer segment actually declined for the third consecutive month.
This is the kind of signal that anomaly detection is designed to catch. Not the dramatic fraud cases or server outages that dominate most articles about the topic, but the quiet, structural deviations in business data that change the meaning of your top-line numbers. The ones that matter most to a small team making decisions with limited data and limited margin for error.
The problem is that anomaly detection has traditionally required either a data scientist who understands the mathematics or an enterprise platform with a six-figure price tag. Neither option works for a 10-person company. But the underlying techniques are more accessible than the industry makes them seem, and a growing number of tools now automate the hard parts.
This guide explains what anomaly detection actually does, walks through the methods that matter most for business data, and shows you how to put them to work without writing algorithms from scratch.
What anomaly detection is (and what it is not)
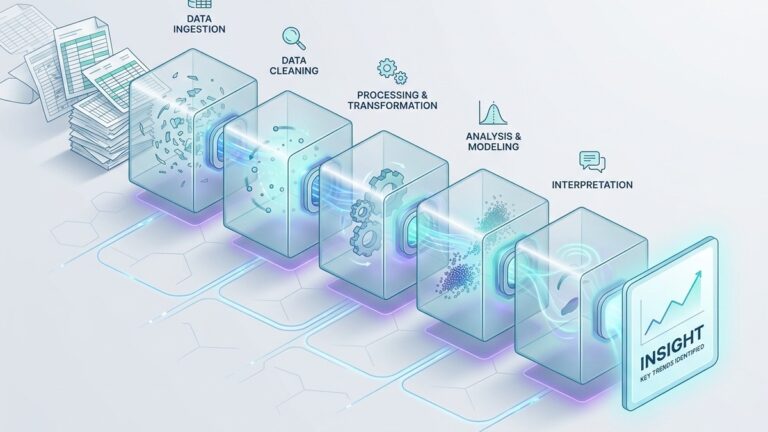
Anomaly detection is the process of identifying data points, events, or patterns that deviate significantly from what is expected. That is the textbook definition, and it is correct but incomplete. In practice, anomaly detection answers a more specific question: “Is this unusual enough that someone should look at it?”
The distinction matters because not every outlier is an anomaly, and not every anomaly is a problem. A customer who spends ten times the average might be your best account, not a data error. A spike in website traffic on Black Friday is perfectly normal in context, even though it is statistically extreme. A slow decline in email open rates over six months is not a single anomalous point at all, but rather a trend that a different kind of analysis should catch.
The field generally recognizes three types of anomalies, a classification that Splunk’s anomaly detection overview lays out clearly. Point anomalies are individual values that fall far outside the normal range, like a single refund that is 50 times larger than your average transaction. Contextual anomalies are values that are only unusual in a specific context, like high server traffic at 3 AM on a Tuesday. Collective anomalies are groups of data points that are individually unremarkable but collectively form an unusual pattern, like a sequence of small transactions from the same account in rapid succession.
For small business analytics, point anomalies and contextual anomalies are the ones you will encounter most often. Understanding the difference helps you choose the right detection method and, just as importantly, avoid overreacting to signals that are not actually signals.
Why dashboards miss anomalies
Standard business dashboards are built to answer predefined questions. “What was revenue last month?” “How many new customers did we acquire?” “What is the conversion rate by channel?” These are important questions, but they share a structural limitation: they show you aggregated metrics on a schedule you defined in advance.
Anomalies, by definition, are things you did not expect. A dashboard designed around monthly revenue totals will never show you that a single day’s transactions were three standard deviations above normal unless someone specifically builds a view for that. A campaign performance dashboard that shows average cost per acquisition will not flag that one specific ad set is quietly spending budget with zero conversions.
This is the gap that anomaly detection fills. Instead of answering the questions you already thought to ask, it surfaces the questions you should be asking but are not.
The practical impact for small teams is significant. A Gartner study estimated that organizations lose an average of $12.9 million annually to poor data quality, and a major contributor is anomalous data that goes undetected because nobody is looking for it. For a small business, the absolute number is lower, but the relative damage is often worse: a billing error that runs uncorrected for three months, a marketing channel that quietly stops converting, or a product with a climbing return rate that nobody notices until inventory is already committed.
The methods that matter for business data
The academic literature on anomaly detection is vast. A 2021 systematic literature review on ResearchGate catalogued dozens of algorithmic approaches across domains from cybersecurity to manufacturing. Most of those methods are irrelevant for a marketing manager trying to spot unusual patterns in campaign data.
For typical small business analytics, four methods cover the large majority of practical use cases. They range from simple enough to implement in a spreadsheet to sophisticated enough to power commercial platforms.
Method 1: Z-score thresholds
The z-score is the simplest statistical approach to anomaly detection and, for many use cases, entirely sufficient. It measures how many standard deviations a data point is from the mean of its distribution. A z-score of 0 means the value is exactly average. A z-score of 2 means it is two standard deviations above the mean, which roughly corresponds to the top 2.3 percent of values in a normal distribution. A z-score of 3 is even more extreme, occurring less than 0.15 percent of the time by chance.
The formula is straightforward: take the value, subtract the mean, and divide by the standard deviation. In a spreadsheet, that is =(value - AVERAGE(range)) / STDEV(range). Any value with a z-score above 2 or below -2 is worth investigating. Values beyond 3 or -3 are almost certainly anomalous.
The strength of z-scores is their simplicity and interpretability. Anyone on your team can understand “this value is 3.2 standard deviations from normal.” The weakness is that z-scores assume your data follows a roughly normal (bell-curve) distribution. Business data frequently does not. Revenue, transaction values, and customer lifetime value are almost always right-skewed, with a long tail of high values. In skewed data, the mean and standard deviation are pulled upward by the tail, which makes it harder to detect anomalies in the body of the distribution.
For symmetric data (like daily website sessions, email open rates, or A/B test conversion rates), z-scores work well. For heavily skewed data (like revenue per customer or order values), you need something more robust.
Method 2: Interquartile range (IQR)
The IQR method is a non-parametric alternative to z-scores, meaning it does not assume any particular distribution shape. It works by finding the 25th percentile (Q1) and the 75th percentile (Q3) of your data, calculating the range between them (IQR = Q3 – Q1), and then defining anything below Q1 – 1.5 * IQR or above Q3 + 1.5 * IQR as a potential outlier. The 1.5 multiplier is the standard threshold established by John Tukey in his foundational work on exploratory data analysis. Using 3 * IQR instead flags only extreme outliers.
The IQR method is what generates the “whiskers” on a box plot, which is why box plots are one of the most useful visualizations for quick anomaly screening. If you have ever looked at a box plot and noticed dots beyond the whiskers, those are exactly the points that the IQR method flags.
This approach handles skewed data better than z-scores because percentiles are not distorted by extreme values the way the mean and standard deviation are. It is also easy to implement: most spreadsheet tools and BI platforms can calculate percentiles natively.
The limitation is that the IQR method is purely univariate. It looks at one variable at a time. If an anomaly only becomes visible when you combine two or more variables (for example, a customer with normal order frequency but unusually high returns), the IQR method will miss it.
Method 3: Isolation Forest
Isolation Forest is a machine learning algorithm specifically designed for anomaly detection, and it represents a genuine conceptual breakthrough in how the problem is approached. The original paper by Liu, Ting, and Zhou (2008) proposed a simple but powerful insight: instead of building a model of what “normal” looks like and then measuring deviation from it, why not directly try to isolate each data point?
The algorithm works by randomly selecting a feature and randomly selecting a split value, then recursively partitioning the data. Anomalies, because they are few in number and different from the majority, tend to get isolated in very few splits. Normal data points, which are clustered together with many similar points, require many more splits before they end up alone. The average number of splits needed to isolate a point across many random trees becomes its anomaly score.
What makes Isolation Forest particularly valuable for business data is that it works across multiple dimensions simultaneously. It can detect a data point that is not unusual on any single metric but is unusual in combination: a customer with average order value, average frequency, and average returns who nonetheless has an anomalous profile because no other customer has that specific combination.
Scikit-learn, the most widely used Python machine learning library, includes a production-ready Isolation Forest implementation. DataCamp has published a practical tutorial that walks through the implementation with real data. For teams without Python experience, several no-code analytics platforms now offer Isolation Forest under the hood as part of their automated analysis.
The trade-off is interpretability. When Isolation Forest flags a data point, it tells you the point is anomalous but does not directly tell you why. You need to examine the flagged point manually to understand which dimensions make it unusual. For small datasets where you can inspect flagged points individually, this is fine. For large-scale automated monitoring, it can create a “now what?” problem.
Method 4: Time series decomposition
The methods above work on static datasets. But much of business data is temporal: daily revenue, weekly signups, monthly churn rates. For time series data, an anomaly is not just “far from the average.” It is “far from what we would expect given the trend, the seasonality, and the recent history.”
Time series decomposition separates a signal into three components: the trend (long-term direction), the seasonal pattern (repeating cycles), and the residual (everything that is left over after you remove trend and seasonality). Anomalies show up in the residual. If the residual for a given day is much larger than typical residuals, something unexpected happened.
The STL decomposition method (Seasonal and Trend decomposition using Loess), documented extensively in Rob Hyndman’s freely available textbook Forecasting: Principles and Practice, is the standard approach. Meta’s Prophet library popularized a Bayesian variant that is particularly good at handling missing data and holidays.
For a small team, time series anomaly detection answers questions like: “Is today’s revenue actually unusual, or is it just a normal Tuesday in a seasonal business?” and “Did that product launch actually change our trajectory, or did we just have a good week?” Without decomposition, you are comparing today’s number to last month’s number and guessing. With decomposition, you are comparing today’s actual value to a model’s prediction of what today should have been, and measuring the gap.
The false positive problem
Every article about anomaly detection eventually has to address false positives, because this is where most implementations fail in practice. A Precedence Research report noted that false positives are the single biggest challenge in practical anomaly detection, driving up analyst workloads and eroding trust in detection systems.
The math explains why. If you flag everything beyond two standard deviations, roughly 5 percent of your data will be flagged as “anomalous” even when nothing unusual is happening. For a dataset with 1,000 data points, that is 50 false alarms. If nobody has time to investigate 50 alerts, the entire system gets ignored, and the real anomalies get missed along with the false ones.
The solution is not to raise the threshold so high that you only catch the most extreme cases. That reduces false positives but also misses the subtle anomalies that are often the most important ones in business data.
Instead, the most effective approaches layer multiple methods together. Flag a transaction as potentially anomalous if it exceeds the IQR threshold, then check whether it is also anomalous in the context of recent time series behavior. If both methods agree, escalate. If only one does, queue for periodic review. This layered approach dramatically reduces false positives while maintaining sensitivity.
QuantumLayers has written about how they apply advanced statistical safeguards including false discovery rate correction and effect size reporting to ensure that automated insights are genuinely significant rather than statistical noise. The principle applies whether you are using their platform or building your own process: statistical significance alone is not enough. You also need to measure practical significance (how large the deviation is in business terms) and apply corrections for the number of tests you are running simultaneously.
Practical implementation for small teams
If you are a small team without a data scientist, here is a realistic path to implementing anomaly detection without building anything from scratch.
Start with z-scores in your existing spreadsheet. Pick your three most important metrics (revenue, conversion rate, customer acquisition cost, or whatever matters for your business) and add a z-score column to your weekly tracking spreadsheet. Flag anything beyond two standard deviations. This takes about 15 minutes to set up and immediately gives you a structured way to notice unusual weeks instead of relying on gut feel.
Add IQR-based screening for skewed metrics. For metrics where z-scores do not work well (typically anything involving money, like order value or revenue per customer), switch to the IQR method. A box plot of the last 12 months of weekly data will instantly show you which weeks were true outliers and which were just normal variation.
Use an analytics platform for multivariate detection. Once you have the habit of looking for anomalies in individual metrics, the next step is detecting anomalies that only appear when you combine variables. This is where no-code platforms earn their value. Tools like Julius AI, which lets you upload data and ask questions in natural language, can flag unusual patterns across multiple dimensions without requiring you to specify what you are looking for. Akkio offers similar capabilities with a focus on predictive modeling. The key is choosing a platform that surfaces why something was flagged, not just that it was flagged.
Build a weekly anomaly review into your routine. The most important step is not technical. It is behavioral. Add a standing 15-minute block to your weekly analytics review where someone looks at flagged anomalies and asks: “Is this real? Is this important? Should we do something about it?” Without this step, even the best detection system produces alerts that nobody reads.
What to watch for when tools do it for you
As more analytics platforms add automated anomaly detection, it is worth knowing what separates good implementations from bad ones.
Good implementations show you the method. When a platform flags an anomaly, it should tell you what method detected it, how extreme the deviation is, and how confident the system is in the finding. A platform that just says “anomaly detected” with no context is asking you to trust it blindly.
Good implementations distinguish between types. A sudden spike is different from a gradual drift. A single unusual data point is different from a cluster of mildly unusual points. The best platforms classify anomalies by type and adjust their recommendations accordingly.
Good implementations account for context. Black Friday should not trigger a revenue anomaly alert. A seasonal business should not flag every slow month. Platforms that let you define business context (known events, seasonal patterns, expected ranges) produce far fewer false positives than those that treat all data as homogeneous.
Good implementations prioritize. Finding 200 anomalies in a dataset is not useful. Ranking those 200 by statistical significance and business impact, and presenting the top five with clear explanations, is. If a tool surfaces more anomalies than your team can realistically investigate, the volume setting is wrong.
The bottom line
Anomaly detection is not a luxury reserved for companies with data science teams. The core techniques, from z-scores to IQR to Isolation Forest, are well established, well documented, and increasingly available through platforms that require no coding.
The real barrier for most small teams is not technical. It is cultural. Building the habit of looking for what is unusual, not just what is expected, requires a shift in how you think about your data. Dashboards answer the questions you asked. Anomaly detection surfaces the questions you did not know to ask.
Start simple. Add z-scores to your weekly metrics. Look at box plots. Flag the outliers and investigate one per week. The patterns you catch will justify every minute you spend looking.
Lurika is an independent publication covering data analytics for non-technical teams. We are not owned by any analytics vendor.